The Best Way to Approach a Zero Trust Architecture


According to a recent survey of U.S.-based IT and security executives, 65% of respondents said that they – or their employees – had been approached by cybercriminals to assist in aiding a ransomware attack against their own organizations.
The Rising Insider Threat, commissioned by Hitachi ID, a sister company of Hitachi Vantara and a global provider of identity and access management (IAM) solutions, polled 100 executives across the country to learn more about the impact of ransomware on business.
Meanwhile, a separate study from Verizon suggested that insiders were responsible for about 22% of all security incidents; but in some industries the number climbs to as much as 50%. Between 2018 and 2020, the report noted there was a 47% increase in the frequency of incidents involving insider threats, which includes both malicious data exfiltration and accidental data loss.
It’s getting hard to trust anyone anymore. The only solution is a Zero Trust Architecture. “Zero Trust” is a security approach that addresses the new network realities of fluidity, openness, and, ultimately, vulnerability by trusting no one – internal or external to your organization.
The basic tenets of Zero Trust Security are:
And the practice is catching on. In the U.S., Zero Trust Architecture has garnered nationwide attention. In May of 2021, President Biden issued a White House Executive Order on Improving the Nation’s Cybersecurity and one of the directives contained in that order was the following:
“The Federal Government must adopt security best practices; advance toward Zero Trust Architecture; accelerate movement to secure cloud services, including Software as a Service (SaaS), Infrastructure as a Service (IaaS), and Platform as a Service (PaaS); centralize and streamline access to cybersecurity data to drive analytics for identifying and managing cybersecurity risks; and invest in both technology and personnel to match these modernization goals.”
And January 26, 2022, the President’s Office of Management and Budget (OMB) issued the Moving the U.S. Government Toward Zero Trust Cybersecurity Principles memorandum to the heads of Executive Departments and Agencies, in which it stated: This memorandum requires agencies to achieve specific zero trust security goals by the end of Fiscal Year (FY) 2024.
The memo also required submission of an implementation plan for FY2022-FY2024 for OMB concurrence, and a budget estimate for FY2024 within 60 days of the issuance of this memo.
Well written, the memo serves as a set of guiding principles that any organization considering a Zero Trust Architecture should review. Of course, any organization planning to do business with the U.S. government will have to implement such an architecture, regardless.
The U.S. government has put a stake in the ground and the movement to Zero Trust Architecture has accelerated.
The traditional perimeter-based approach to security depended on firewalls, virtual private networks (VPNs), and web gateways to separate trusted users from untrusted users. Unfortunately, today we must protect against the “trusted” users, as well; not because people are less trust-worthy, but because the attack surface is expanding so rapidly it is increasingly difficult to define meaningful boundaries.
Systems and data that once resided inside the traditional data center network perimeter are now being moved into the cloud. What used to be deployed on a single server is now operated in hundreds of containers or microservices. Code development is now an automated DevOps process using third party code and data lakes are spread from core to edge to cloud. While this compute and data model has enabled greater agility, productivity, and opportunity for organizations, it has opened the perimeters making it impossible to trust anyone or anything.
Two key elements of Zero Trust Architecture are the technologies and processes that make up Identity Access Management (IAM) and Perimeter Access Management (PAM).
IAM is the security discipline that makes it possible for the right entities (people or things) to use the right resources (applications or data), without interference, using the desired devices. IAM is comprised of the systems and processes that allow IT administrators to assign a single digital identity to each entity, authenticate them when they log in, authorize them to access specified resources, and then monitor and manage those identities throughout their lifecycle while in the system.
PAM is a combination of tools and technologies used to secure, control, and monitor access to an organization's critical information and resources.
Privileged user accounts are significant targets for attacks as they have elevated permissions, access to confidential information and the ability to change settings. Implementing a PAM system helps organizations effectively monitor the entire network and provides insight into which users have access to what data. PAM can thwart ransomware attacks by denying them the permissions that they need to do their dirty work. Privileged access now extends to the cloud, big data projects, and DevOps automation, as well as hundreds of containers or microservices in hybrid cloud environments instantiating what used to be a single server in a “controlled” and “safe” data center.
Going forward, Zero Trust Architecture will require enhancements to IAM and PAM that analyze the context in which the authentication is requested. Users will have to be able to request elevated rights just-in-time through self-service workflows such as the user, resource and roles requested, location, and presence of an identity cookie — so that approvers can make informed grant-or-deny decisions.
Approvers should be risk-aware, using modern machine learning (ML) and user and entity behavior analytics for even greater assurance. Just-in-time privilege grants users just enough (least) privilege for only as long as they need to perform a specific job function. Governing access through just-in-time and just enough privilege allows access to be temporary and time-bound with request and approval workflows.
Zero Trust Architecture doesn’t require a “rip and replace” implementation and should be done incrementally. Organizations can start with what they already have in place and implement it in phases as resources and priorities permit. The first step is to assess of what’s in place and what will be needed.
Start your Zero Trust Journey today.
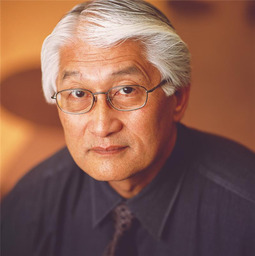
Hu Yoshida spent 24 years at Hitachi Vantara helping define technical direction and enabling customers to address their digital transformation needs. He is widely known in the industry and was instrumental in evangelizing Hitachi's unique approach to storage virtualization.